Introduction to Amazon Cognito
Amazon Cognito lets users sign in/sign up to the web and mobile applications. It provides access control of authentication and authorization to the users over the web application by setting specific permissions for accessing the resources.
Click here to Understand Amazon Cognito Authentication.
Key factors of Amazon Cognito
Authentication is an extra layer of protection for applications where users can authenticate through
- username and password
- OTP-based authentication
- Multi-factor authentication
Authorization is when a user wants to access private resources like a database or REST API, for which they need the authorization to access the secured resources.
The user pool is like an active directory of the users to sign in/sign-up for the applications and the identity pool is to grant access to the AWS resources. A user pool is a directory that stores a user’s login credentials, which can be used for further login validation. Amazon Cognito provides temporary login credentials with limited access to AWS resources.
Users can sign into Cognito through social networks (Facebook, Google, etc.,) and Federated identity providers.
In the user pool, we can customize the authentication flow. For example, the user can log in to the application without a password. For this, the user needs to enter the username and then click on sign-in, it will send OTP to the respective email or phone to authenticate, and then the user can log in to the application.
For the Identity pool, if the user is authenticated, we can grant access to the resources. But if the user is not authenticated, we can provide temporary guest access. It also offers role-based access to AWS resources.
When the device is online, the data is automatically synced with AWS. It allows the users to access the data from multiple devices. To activate Amazon Cognito sync organization must set up an identity pool.
In Amazon Cognito, we can use the lambda function to migrate complete users into the user pool from different directory services without resetting their passwords.
- Cloud Migration
- Devops
- AIML & IoT
How the AWS Cognito Authentication works?
a) First the user sign-in to the user pool.
b) Once the authentication is successful, the user receives a user pool token.
c) With the help of the identity pool, the app exchanges tokens for AWS credentials.
d) Now the user can use these AWS credentials to access the AWS resources.
Amazon Cognito Security
- It follows standard-based authentications like OpenID Connect and SAML 2.0 & 0Auth 2.0
- Amazon Cognito follows security standards for your apps and users – HIPAA eligible and PCI DSS, SOC, and ISO/IEC 27001, ISO/IEC 27017, ISO/IEC 27018, and ISO 9001
Pricing for Amazon Cognito
AWS free tier has 50000 MAUs (Monthly Active User) who sign in with the user pool and 50 MAUs for users who are federated through identity providers.
Setup Guide for Amazon Cognito User pool and Identity pool
Step 1: Log in to AWS Console and type AWS Cognito in the search bar.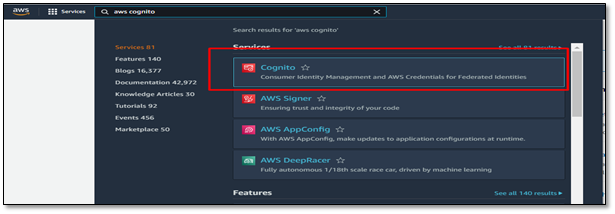
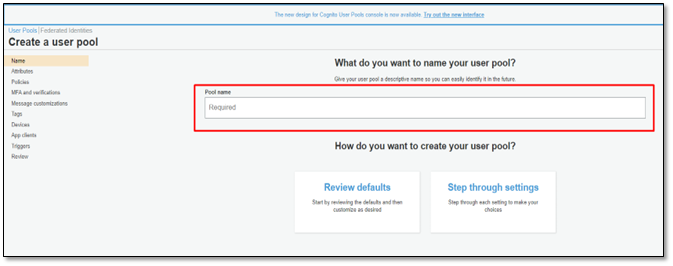
Step 2: Click on Manage user pools.
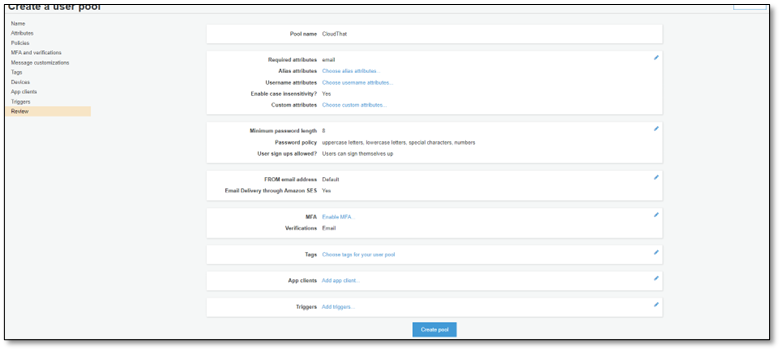
Step 4: Fill up the below details and Click on Create Pool
- Create pool and attributes
- Customize password policy
- Configure SES (Simple Email Service) and MFA (Multi-Factor Authentication) for additional security
- Configure App client
- Click on create a pool
Step 5: Pool Id and Pool ARN are created after submitting the details.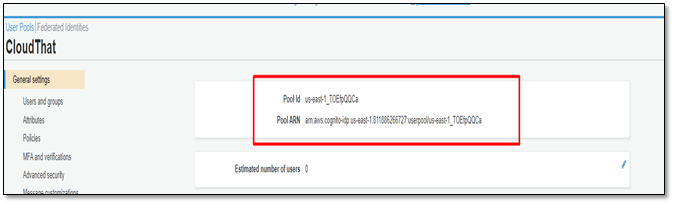
Step 6: To create users, click on the user and group option.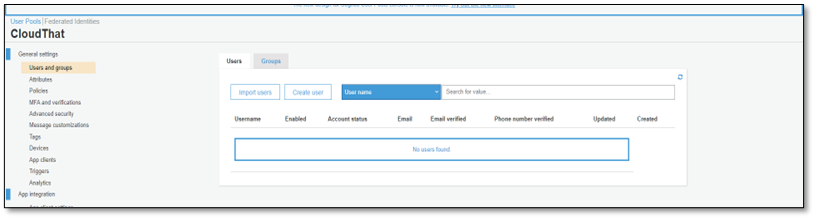
Step 7: Click on create the user and provide a username, temporary password, phone number, and email ID.
Step 8: To create an Identity pool, click on Federated identity, and give a new identity pool name (pool name is unique).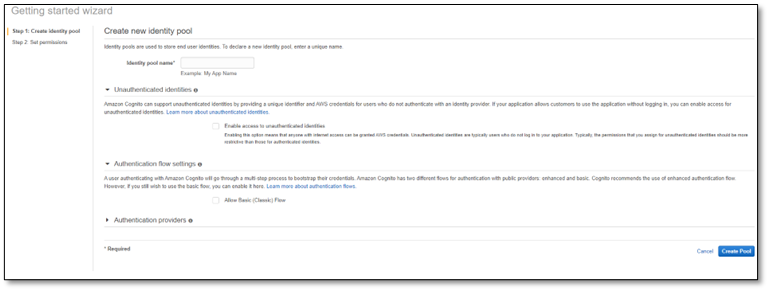
Step 9: Select the authentication provider and public provider you want. We can add multiple app providers.
Step 10: After selecting create the pool, it creates an Identity pool ID and region.
Conclusion
Amazon Cognito is a secure and scalable user directory service that uses standard-based authentication through social and enterprise identity federations. It provides access control to the AWS resources and easy integration with your application.
If you have any comments or questions about Setup Guide for AWS Cognito User Pool or Identity Pool or any other service, please feel free to comment here. I will be available to answer any doubts or queries.
Get your new hires billable within 1-60 days. Experience our Capability Development Framework today.
- Cloud Training
- Customized Training
- Experiential Learning
About CloudThat
We here at CloudThat are the official AWS (Amazon Web Services) Advanced Consulting Partner and Training partner and Microsoft gold partner, helping people develop knowledge on the cloud and help their businesses aim for higher goals using best in industry cloud computing practices and expertise. We are on a mission to build a robust cloud computing ecosystem by disseminating knowledge on technological intricacies within the cloud space. Our blogs, webinars, case studies, and white papers enable all the stakeholders in the cloud computing sphere.
CloudThat is a house of All-Encompassing IT Services on the Cloud offering Multi-cloud Security & Compliance, Cloud Enablement Services, Cloud-Native Application Development, OTT-Video Tech Delivery Services, Training and Development, and System Integration Services,. Explore our Consulting and Expertise site.
FAQs
1. What are unauthenticated users?
ANS: – For Users who don’t authehttps://www.cloudthat.com/consulting/nticate with any identity provider, if users want access to the resources, we can define an IAM role with limited permissions to access the backend AWS resources.
2. What is a User Pool?
ANS: – A user pool is a directory that stores a user’s login credentials, and we can create a User Pool using the AWS console, AWS CLI, or AWS SDK.
WRITTEN BY Ankith Pokala


 Login
Login


 July 26, 2022
July 26, 2022
 PREV
PREV










Comments