- Consulting
- Training
- Partners
- About Us
x
| TABLE OF CONTENT |
| 1. Introduction |
| 2. Configuring AWS |
| 3. Configuring the Firewall |
| 4. Checking the connection status |
| 5. Summary |
| 6. About CloudThat |
| 8. Frequently Asked Questions |
A site-to-site VPN connection is usually done between two remote networks: a cloud provider and an on-premises network. It helps secure private communication between the remote resources or connects multiple resources in different office locations. IP sec connections work with the help of key exchange, authentication, and encryption providing enhanced security for data transfers.
This type of connection is permanent, which means it is generally a long-lived connection. However, other network connections like remote access VPN are temporarily used to connect to applications for a short time.
Some Benefits of IP-sec site to site VPNs are:
Today I will explain in detail the step-by-step procedure to connect an AWS site-to-site VPN connection to any third-party firewall or network environment. These will consist of basic steps to connect almost any local on-premises network to AWS. In today’s example, I would work with the SOPHOS-XG firewall.
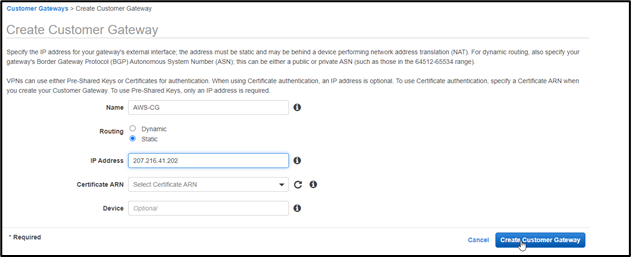
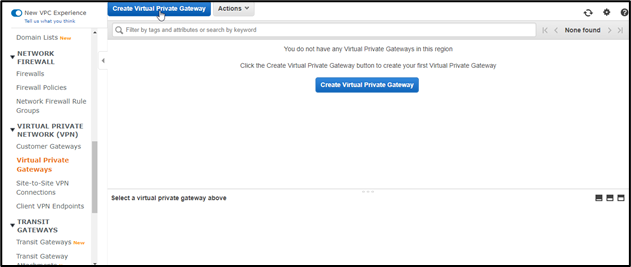
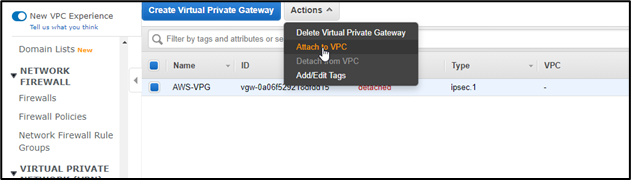
Let us go to the required steps for connecting AWS VPN to a third-party network environment:







Here at Sophos-XG, you also need to configure a phase-2 with the same settings
You can find other information needed in the configuration file which we downloaded in the previous step
Everything is done and fulfilled according to the basic configuration needed for your VPN tunnel. The connection status will be UP and Running, which will also reflect in the AWS site to site VPN connections page.
We have successfully configured a site-to-site VPN connection between AWS and an on-premises network. Your remote network can be anything from a private network environment to a paid firewall environment. AWS provides a generic configuration file that contains detailed information about your AWS side VPN. You can choose between vendors like Cisco, Fortinet, Palo Alto, Juniper, etc.
You can start using your up and running tunnel to transfer data, data migration, network drives sharing, and more. VPNs make the transfer secure, highly available, and reliable.
We here at CloudThat are the official AWS (Amazon Web Services) Advanced Consulting Partner and Training partner and Microsoft gold partner, helping people develop knowledge on cloud and help their businesses aim for higher goals using best in industry cloud computing practices and expertise. We are on a mission to build a robust cloud computing ecosystem by disseminating knowledge on technological intricacies within the cloud space. Our blogs, webinars, case studies, and white papers enable all the stakeholders in the cloud computing sphere.
Feel free to drop a comment or any queries that you have regarding AWS services, cloud adoption, consulting and we will get back to you quickly. To get started, go through our Expert Advisory page and Managed Services Package that is CloudThat’s offerings.
AWS VPN establishes connectivity between various networks that includes on-premises networks, remote workplaces, client devices, and AWS global network. The AWS VPN consists of two main services: 1) AWS Client VPN and 2) AWS site-to-site VPN. AWS client VPN helps to manage remote access by connecting users with AWS or on-premises resources. AWS Site-to-Site VPN establishes encrypted tunnels between Amazon Virtual Private Clouds and end-user networks.
Yes, AWS VPN comes with additional encryption, integrity, and key exchange algorithms. The advanced algorithms ensure higher security and protect your data, assure higher performance for faster transfer rates, and help in meeting compliance requirements with ease.
Our support doesn't end here. We have monthly newsletters, study guides, practice questions, and more to assist you in upgrading your cloud career. Subscribe to get them all!
Hitesh Lodha
Mar 16, 2022
Very well explained 👍😇
Akshay Mishra
Mar 24, 2022
Thank you Hitesh